As users constantly share data access, Torsion delivers automated visibility and control of ‘who has access to what’ in Microsoft 365. Let us walk you through the key stages of How Torsion Works.
How Torsion Works
Step 1
Firstly, we create your unique and isolated Torsion tenant, then it takes just a few minutes to connect your Torsion tenant to your Microsoft 365 tenant.
Torsion builds a complete index of every file, folder, site and Team, every user, every instance of a person having access to information, and every instance of a person actually accessing information. It crawls the data, ingests the activity logs and plugs into Active Directory, keeping the index constantly up to date. Indexing takes between a couple of hours and a couple of days.
Torsion lights up and is now ready to go.
Step 2
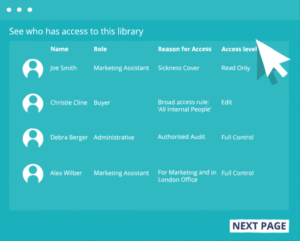 Immediately, Torsion provides granular visibility into ‘who has access to what’.
Immediately, Torsion provides granular visibility into ‘who has access to what’.
It covers every possible mechanism of someone getting access to data in Microsoft 365. Including the many complex, technical ways which aren’t visible to users or most casual administrators.
Take any file, folder, site or Team, and Torsion shows you instantly who has access, who gave it to them, how, when and the business reason why they have access. For data owners as well as admins.
It makes it simple to slice and dice, to explore and run reports on all of it. Just about any question around ‘who has access to what’ is answered in seconds. Some examples:
User Access
What data does user John Smith have access to?
Broken Permissions
Which Teams have files with different permissions to the Teams they’re in?
External Sharing
Which files were externally shared last week?
Nested Access
How many people have access to the data in a site (not just the site itself)?
Suspicious Sharing
Which data sharings are suspicious or unusual?
Who Has Access
Pick any file, see exactly who has access, including all the hidden ways.
Change Over Time
How has access to a file changed over time?
Reasons for Access
See the business reasons why people have access to anything.
Step 3

After you get visibility of data access, you need to get it under control and keep it under control. This entire process is now automated with Torsion.
Torsion is the centrepiece of an effective strategy for Data Access Governance in Microsoft 365. Setting up its powerful access control capabilities is simple and quick (days or weeks, not months or years), and then it basically runs itself.
Torsion includes many powerful features which help you keep control of access:
Fix Inappropriate Access
Automatically detects inappropriate access (e.g. this person has access to this document, and its not OK), then seamlessly engages with the data owner to automatically fix it.
Automated Permissions
Automatically grants and revokes detailed permissions as people change roles and assignments, customers and partners come and go, and your business constantly changes.
Enforce Policies
Enforces all your policies for what kinds of access, users, data and behaviour are OK, or not. The moment a policy line is crossed, Torsion automatically detects it, and works with the data owner to fix it.
